LockBridge Secures Peer-to-Peer File Transfers With Zero-Trust Access
Ellen Smith — May 2, 2025 — Tech
References: lockbridge
LockBridge is a secure file-sharing platform built for businesses focused on data protection and compliance. The tool supports real-time peer-to-peer file transfers and encrypted storage, utilizing a zero-trust security model. LockBridge applies end-to-end encryption by default, ensuring data is protected both in transit and at rest.
Its role-based access control allows administrators to assign and manage permissions based on user roles, adding a layer of operational oversight and reducing risk. This makes the platform suitable for teams with strict data governance requirements, particularly in industries such as legal, finance, or healthcare. LockBridge’s infrastructure avoids centralized storage bottlenecks, which can reduce the likelihood of large-scale data breaches. For companies managing sensitive information, the solution balances usability with enterprise-grade security protocols.
Image Credit: LockBridge
Its role-based access control allows administrators to assign and manage permissions based on user roles, adding a layer of operational oversight and reducing risk. This makes the platform suitable for teams with strict data governance requirements, particularly in industries such as legal, finance, or healthcare. LockBridge’s infrastructure avoids centralized storage bottlenecks, which can reduce the likelihood of large-scale data breaches. For companies managing sensitive information, the solution balances usability with enterprise-grade security protocols.
Image Credit: LockBridge
Trend Themes
-
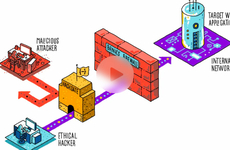
Zero-trust Security — The adoption of zero-trust security models is transforming data protection by eliminating implicit trust, ensuring all users and endpoints are verified continuously.
-
Role-based Access Control — Role-based access control is redefining operational oversight in businesses by enabling customized permissions tailored for different user roles, thereby improving compliance and governance.
-
Decentralized File Storage — Decentralized file storage solutions are mitigating risks of large-scale data breaches by reducing dependence on centralized servers, enhancing data security, and resilience.
Industry Implications
-
Data Protection Software — Innovations in data protection software are crucial for enterprises needing advanced security protocols, especially those handling sensitive and high-stakes information.
-
Legal Technology Solutions — The legal industry is increasingly integrating secure file-sharing platforms, revolutionizing document exchange and ensuring adherence to stringent confidentiality mandates.
-
Healthcare IT Security — Healthcare IT is advancing with encryption and secure file transfer solutions, improving patient data protection while maintaining compliance with healthcare regulations.
3.2
Score
Popularity
Activity
Freshness